trusted cybersecurity solutions for your organisation
We enable small and medium-sized businesses benefit from innovative technologies, achieve desired growth and scale, whilst remaining secure and compliant.
Using the best tools, we offer a comprehensive IT systems security audit and gap analysis, against industry best security practices , and propose the most innovative remedial solution and security strategy.
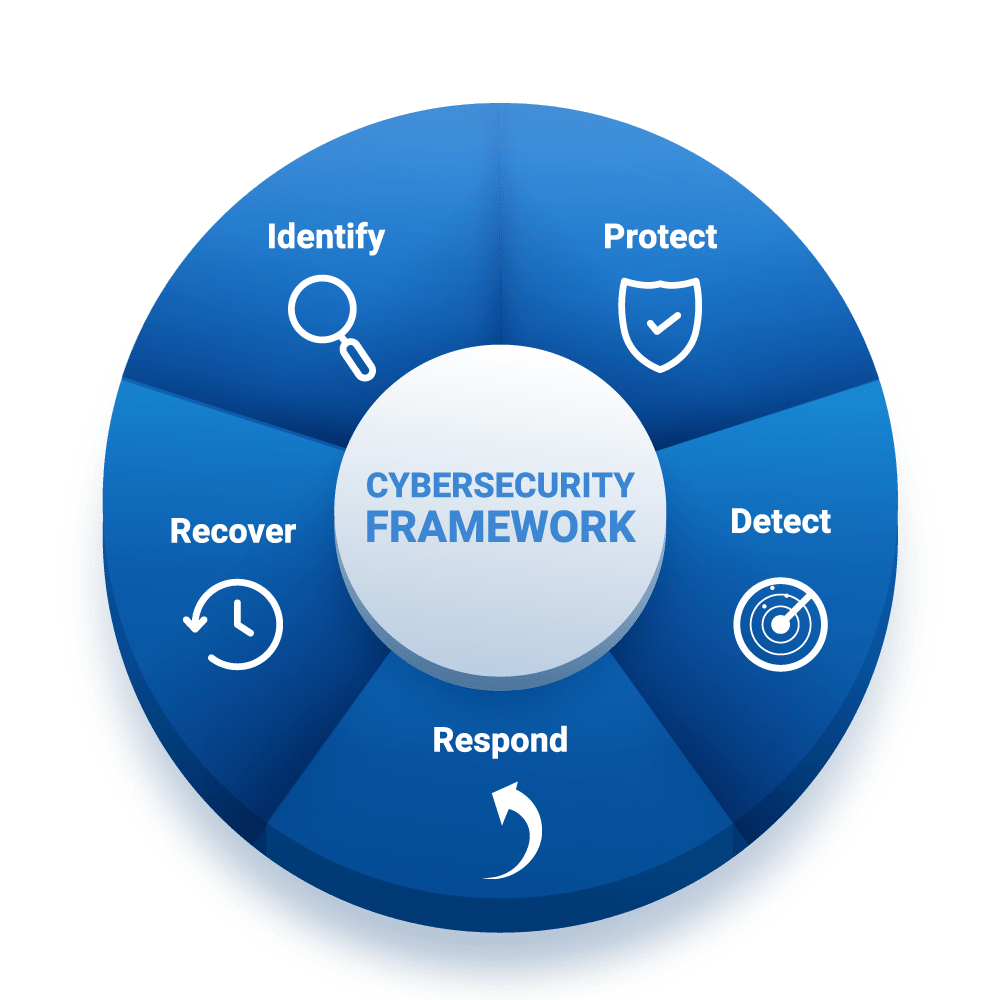
Our approach is simplified and personalised. It is a people, process and technology strategy. We assist you to set up and implement the right policies, processes and technologies to protect your systems, and follow through with training your personnel to fully engage with a sound cybersecurity posture management.

IDENTITY AND ACCESS MANAGEMENT
We implement the most adaptive, optimised and scalable access control strategy for your organisation’s workflow. It cannot be overemphasised that weak access control, poor configuration management, and human error account for most cybersecurity breaches.
RISK ASSESSMENT & COMPLIANCE
A comprehensive risk assessment, security audit and gap analysis, leading to secure by design and secure by default solutions, that meet or exceed industry best practices and comply with relevant regulations. We assist you achieve ISO 27001 and UK Cyber Essentials certifications , as well as EU NIS2, and GDPR compliance requirements.
BACK UP AND STORAGE
On offer is a very cost effective storage and back up solutions for your workloads curated from our partner organisations, seamlessly integrated with our incident response and disaster recovery modules.
DATA LOSS PREVENTION
We classify and protect your most sensitive and critical data from loss, theft, breaches and exfiltration through the deployment of sound process, encryption and AI/Machine learning enhanced technologies.
NETWORK SECURITY
With a combination of automation and human direct oversight from our top professionals , your network is constantly scanned and secure from unauthorised access and intrusions.
DISASTER RECOVERY
In the event of an untoward incidents, you are rest assured of the restoration of your production systems in record time with the help of our disaster recovery plan. That is possible because we have already planned for incidents well ahead of time and it has been well rehearsed and internalised between our both organisations, with your people empowered with the right knowlegde and right instincts.
END-POINT SECURITY
We deploy the best performing End-point detection and response solutions to secure devices in your network. With a 24/7 asset discovery and inventory and a continuous view in real time and all the time into your IT estate, you are guaranteed the best possible odds against breaches and cyberattacks.
FIREWALLS & INTRUSION MANAGEMENT
We have a portfolio of Managed Detection and Response (MDR) software solutions for adaptive intrusion threat detection and response.
INCIDENT RESPONSE & 24/7 SOC
By way of AI-assisted software solutions combined with manned 24/7 SOC we provide an adaptive intrusion threat detection and response. This means our clients can sleep easy, in the confidence of secure mission-critical production systems.

About
Our Security Services & Solutions
We pride in the simplicity and adaptiveness of our approach to cybersecurity. It is personalised. In line with research evidence on what works best, we review your organisation’s policy and processes, elicit gaps and resolve these using the best available and the most cost effective solutions, leaving your IT systems secure and resilient.
Through innovative training methods and simulations, we transform your people to become a pillar of strength rather than a point of weakness in the organisation’s cybersecurity posture.

Our Security Toolkit including Free Resources
We offer our clients a free exploratory consultation, free cybersecurity awareness training including gamified simulations on social engineering techniques using Webroot.
With an array of tools and a collection of the best technologies in the field of cyber defence, we guarantee the best fixes for a secure IT infrastructure and system, so that you really only pay for the fixes and not for the diagnostics!
Active Defence
Proactively Search for and Eliminate Vulnerabilities
Through policy and process review, risk assessment, testing and exercising, we invariably bring to light every security gap in your systems and fix these by deploying best practice process and best available technologies adapted to your organisation’s workflow.